Security Guides
Expert insights, tutorials, and best practices to help you secure your digital life.

How Long Does It Take to Crack Your Password? (2025 Benchmarks)
Think your 8-character password is safe? Think again. We analyze 2025 GPU benchmarks to show exactly how fast a hacker can crack your credentials using modern hardware.
Credential Stuffing Attacks: How They Work & How to Prevent Them
Why do hackers target accounts that haven't been breached? Because of Credential Stuffing. Learn how attackers weaponize password reuse and how to stop them cold.

The Ultimate Guide to Two-Factor Authentication (2FA) & MFA
Passwords aren't enough anymore. Learn the difference between SMS, TOTP apps, and Hardware Keys—and why enabling 2FA is the single most important step for your digital security.

The End of Security Questions: Better Alternatives for Account Recovery
Your mother's maiden name isn't a secret; it's public record. Learn why Knowledge-Based Authentication (KBA) is a security vulnerability and what NIST recommends using instead.
NIST Password Guidelines 2025: Complete Implementation Guide
Learn how to implement NIST SP 800-63B password standards: eliminate complexity rules, add breach screening, and improve security with evidence-based practices.
Password Entropy 101: Why Length Beats Complexity Every Time
Stop forcing users to use special characters. Learn the math behind password entropy and why a long phrase like 'correct-horse-battery-staple' is mathematically stronger than 'Tr0ub4dor&3'.

Understanding Salt & Hashing: How Websites Store Your Passwords
When you sign up for a website, they (hopefully) don't save your password. They save a 'Hash.' Learn the difference between Encryption, Hashing, and Salting—and why it matters.

SOC 2 Type II: The Definitive Guide to Access Control & Auth
Preparing for a SOC 2 audit? Learn exactly what auditors look for in Access Control (CC6) and Logical Access (CC6.1), from onboarding checklists to quarterly access reviews.

Implementing Single Sign-On (SSO): Pros, Cons, and Best Practices
Managing 50 different logins for every employee is a security nightmare. Learn how SSO works, the difference between SAML and OIDC, and why it is the ultimate upgrade for enterprise security.

My Email Was In a Data Breach: 5 Immediate Steps to Take
Don't panic. Just act. If your email appeared in a 'Have I Been Pwned' alert or a dark web scan, here is your step-by-step battle plan to lock down your identity.

HIPAA Compliant Passwords: What Healthcare Providers Need to Know
Stop worrying about audits. Here is the definitive guide to HIPAA password requirements for 2025, covering ePHI protection, multi-factor authentication, and access controls for healthcare.

Cloud vs. Local Password Managers: Which is Safer?
Should you trust the cloud (1Password, Bitwarden) or keep it offline (KeePass)? We break down the security trade-offs, the 'LastPass' incident, and which method is right for your threat model.

PCI DSS Password Requirements: The 2025 Compliance Checklist
Stop guessing with auditors. Here is the plain-English checklist for PCI DSS v4.0 password requirements, including the new rules on 12-character minimums and the death of mandatory rotation.

Why Mandatory Password Expiration Is Dead (And Dangerous)
Still forcing users to change their password every 90 days? You are actually making your organization less secure. Here is the science (and the NIST standards) explaining why rotation is dead.
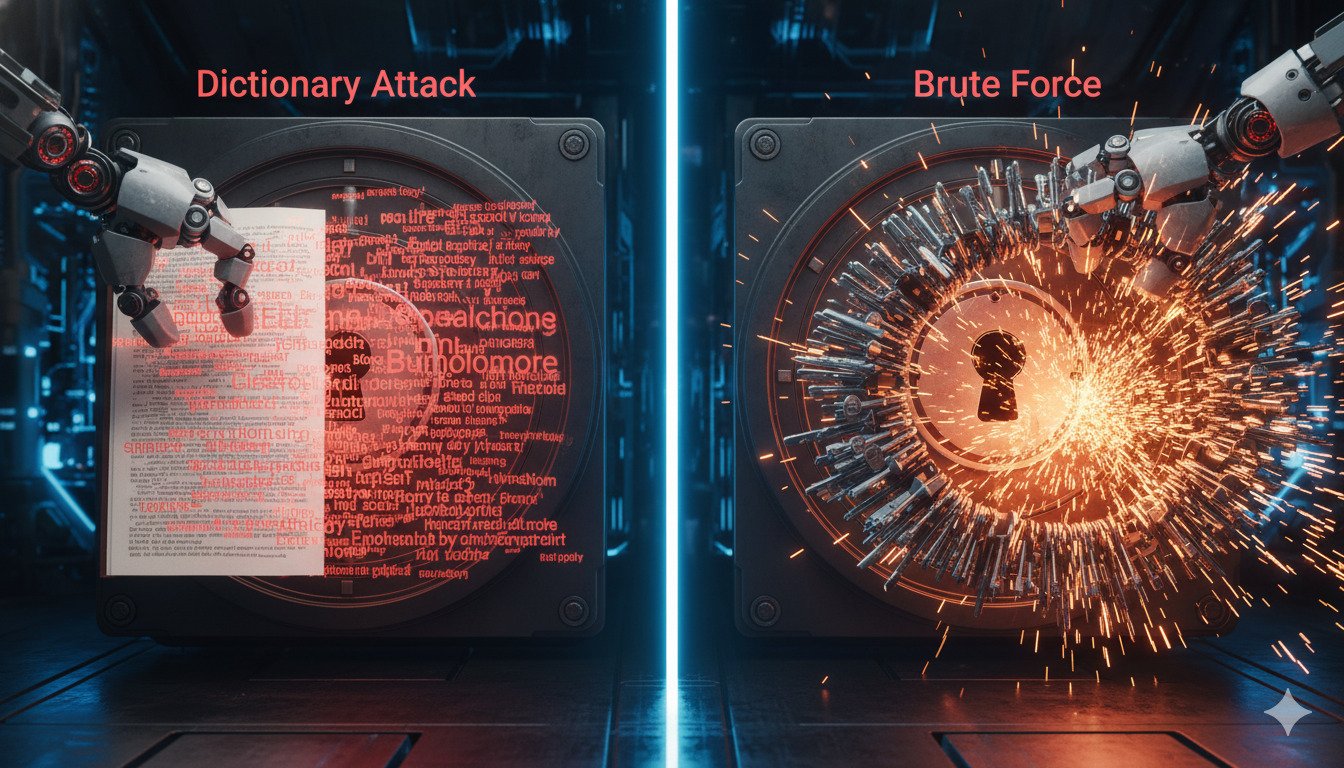
Dictionary Attacks vs. Brute Force: Understanding the Difference
Not all hacks are the same. Learn the difference between the 'smart' Dictionary Attack and the 'dumb' Brute Force attack—and how to build a password that beats both.
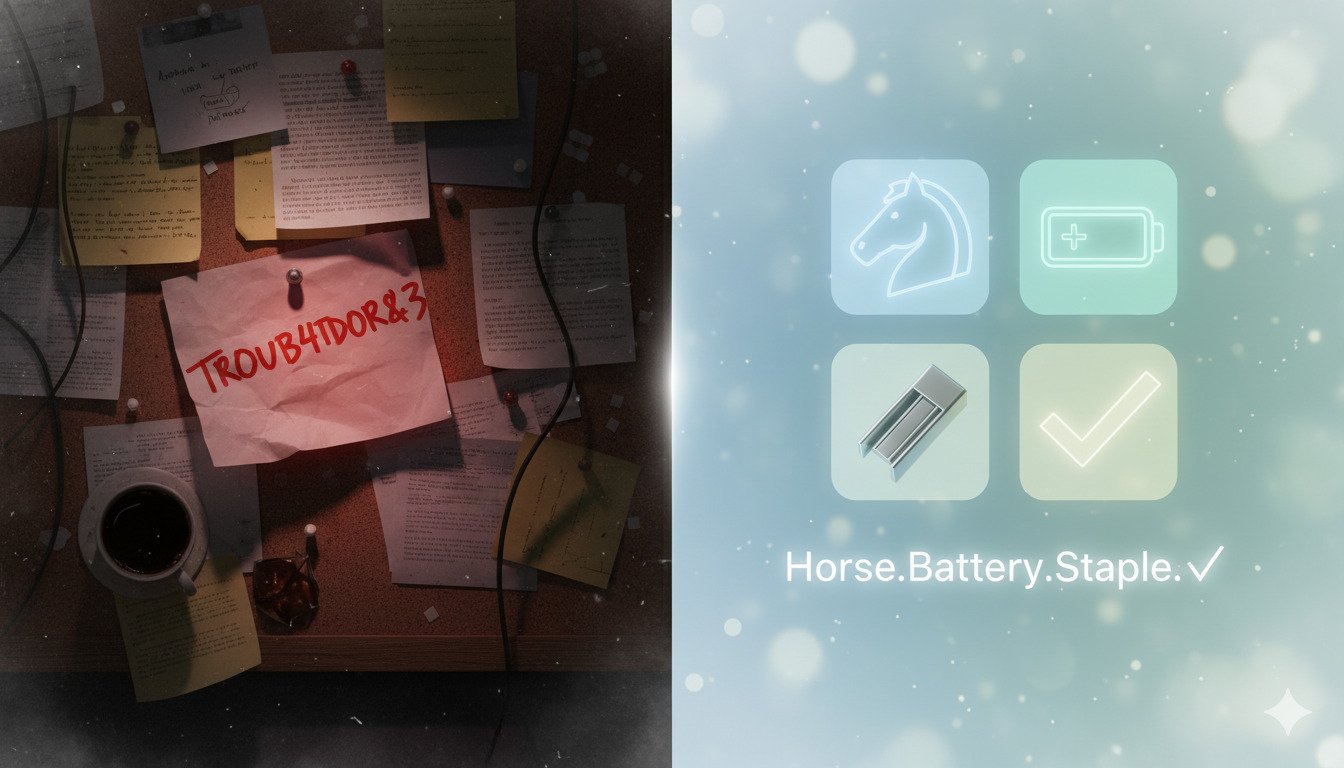
Passphrases vs. Passwords: Why You Should Switch Today
Complexity is out. Length is in. Learn why a random sentence like 'correct-horse-battery-staple' is more secure and easier to remember than your current complex password.
